Security Product Migration and Interoperability
Solution Summary
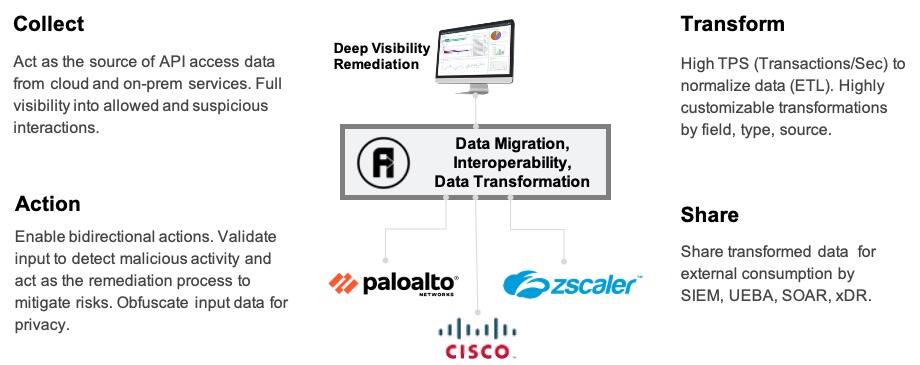
USE CASE: DEEP VISIBILITY AND REMEDIATION
- Transform data from external sources for consumption into a security analytics engine.
- Provide deep visibility into API communications (service frontend for Kubernetes, Service, Mesh, Functions)
- Remediate malicious activity and vulnerable hosts programmatically
USE CASE: DATA TRANSFORMATION
Transform data from external sources for consumption into a security analytics engine.
- Collect and transform log and event data by field, keyword, format into the Security engine data format
- AutoFlow can collect log when deployed inline and remotely via API interaction (Splunk, Elastic)
- Forward select logs to the security analytics engine
USE CASE: API LAYER, INTEROPERABILITY
Provide deep visibility into API communications (service frontend for Kubernetes, Service, Mesh, Functions)
- Make visible shadow APIs
- Report on Shadow API use
- Log API interactions
- Make visible your API attack footprint
- API Discovery
- Log API communications
USE CASE: REMEDIATION OF MALICIOUS ACTIVITIES
Remediate malicious activity and vulnerable hosts programmatically
- Create SOAR workflows to accelerate incident response
- Security engine signals to AutoFlow API to delete malicious sessions or apply custom session routing actions (e.g. direct malicious hosts to non-production services)
- AutoFlow can apply input validation and keyword matching rules to detect malicious activity
0 Comment
-
Leave A Comment :

